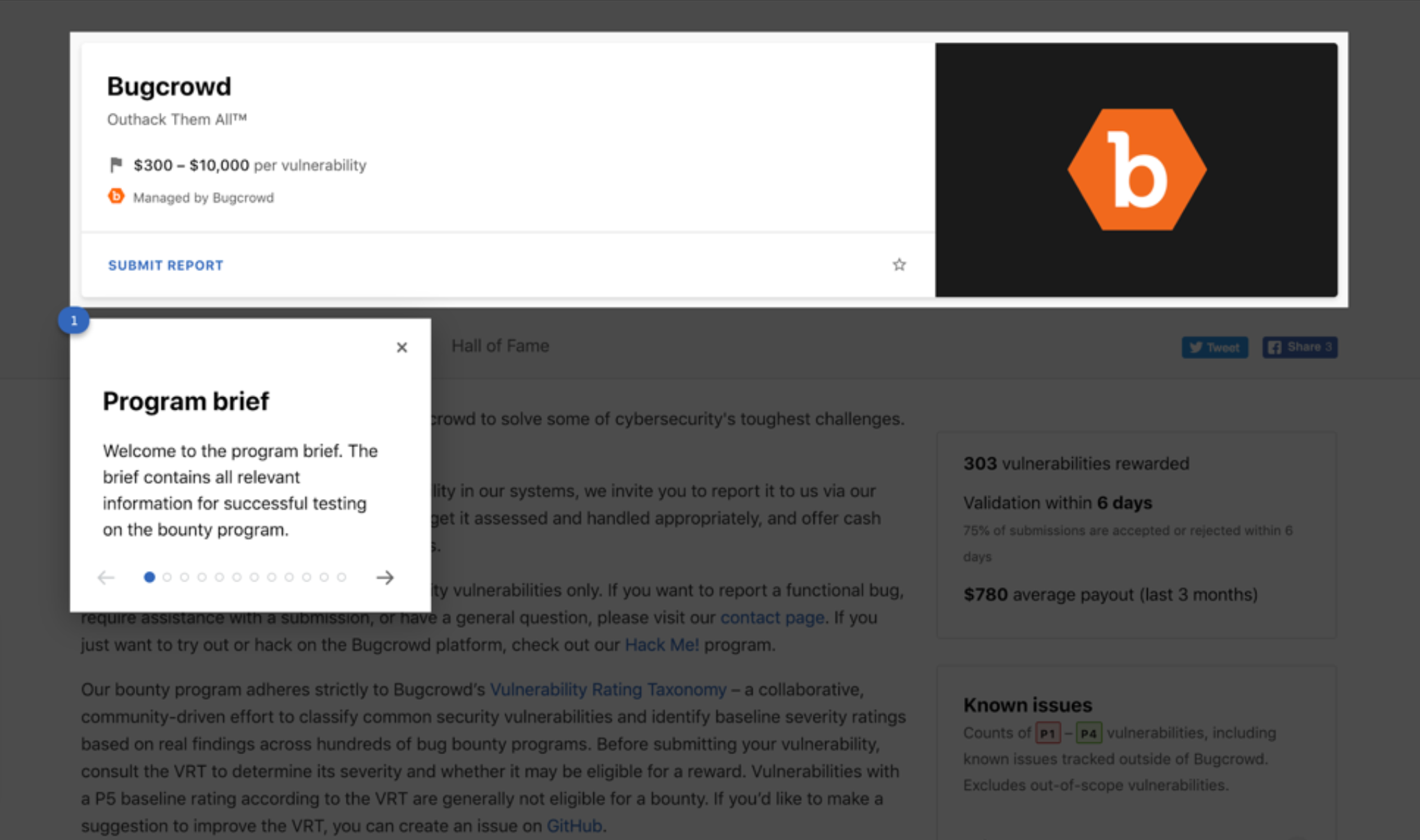
- Viewing the Bounty Brief
- Program Brief header
- Identifying a Managed by Bugcrowd program
- Following a Program
- Reward Ranges
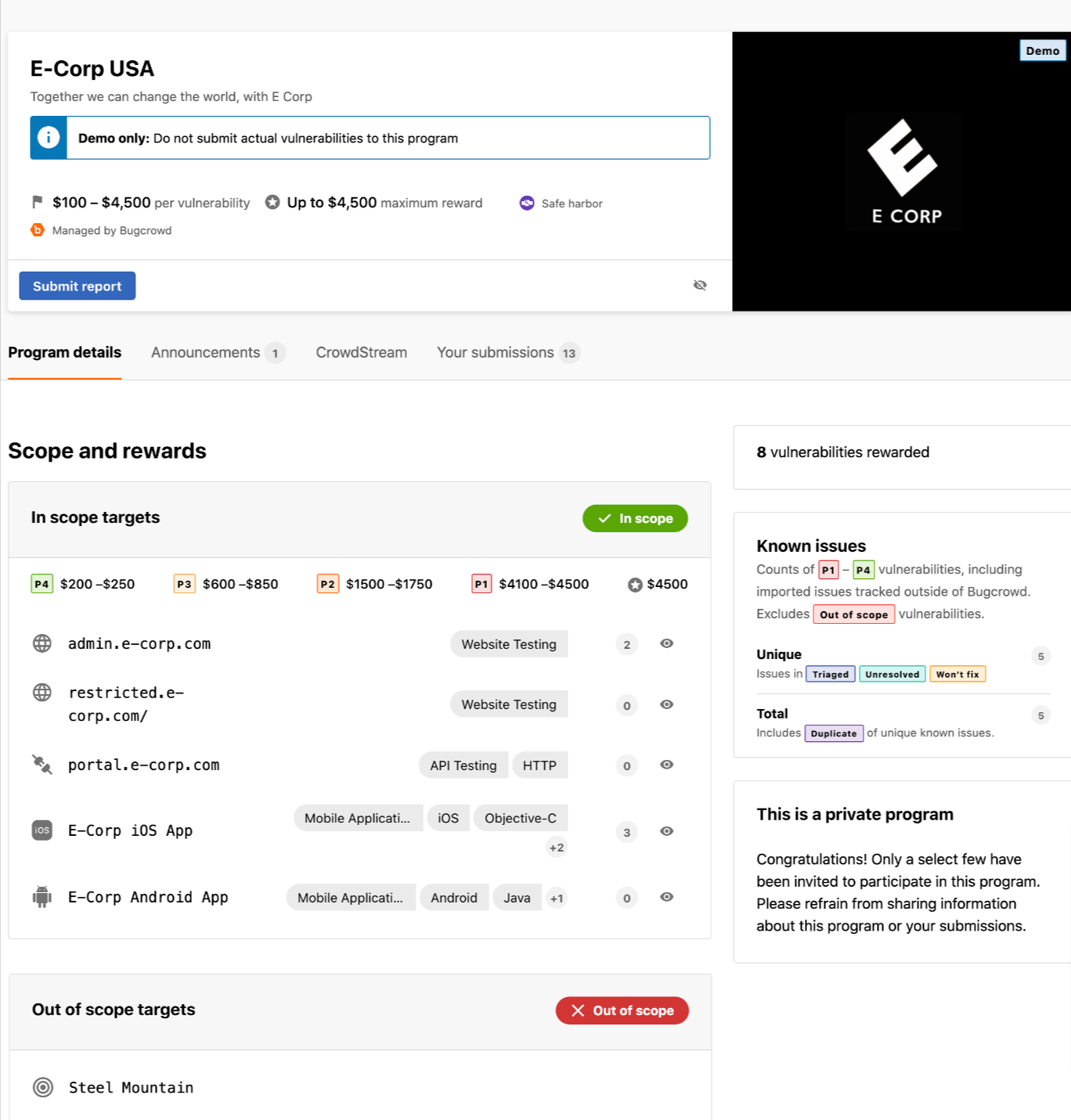
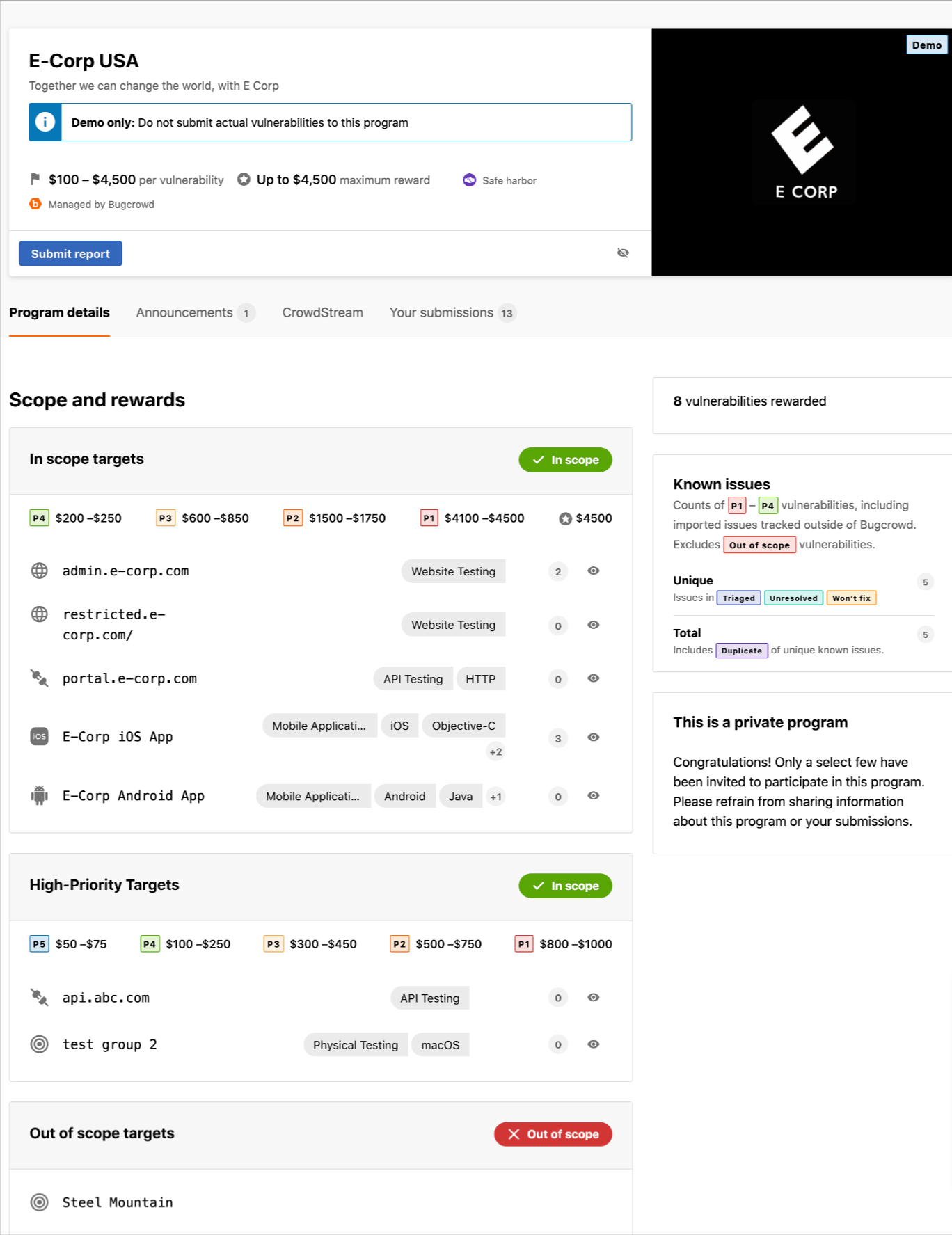
- Scope and Rewards
- Program Rules
- Program Updates
- Viewing the Program’s Statistics
- Viewing Known Issues
- Hall of Fame
A program’s bounty brief provides all the information you need to know about the program, such as the targets, goals, and scope. It outlines the company’s expectations. You must thoroughly review the bounty brief before you start working on a program.
The brief also sets your expectations for rewards, indicating whether you can earn cash rewards for your vulnerability reports, what the reward range would be, and the time expected for your submission to be reviewed and outcome determined.
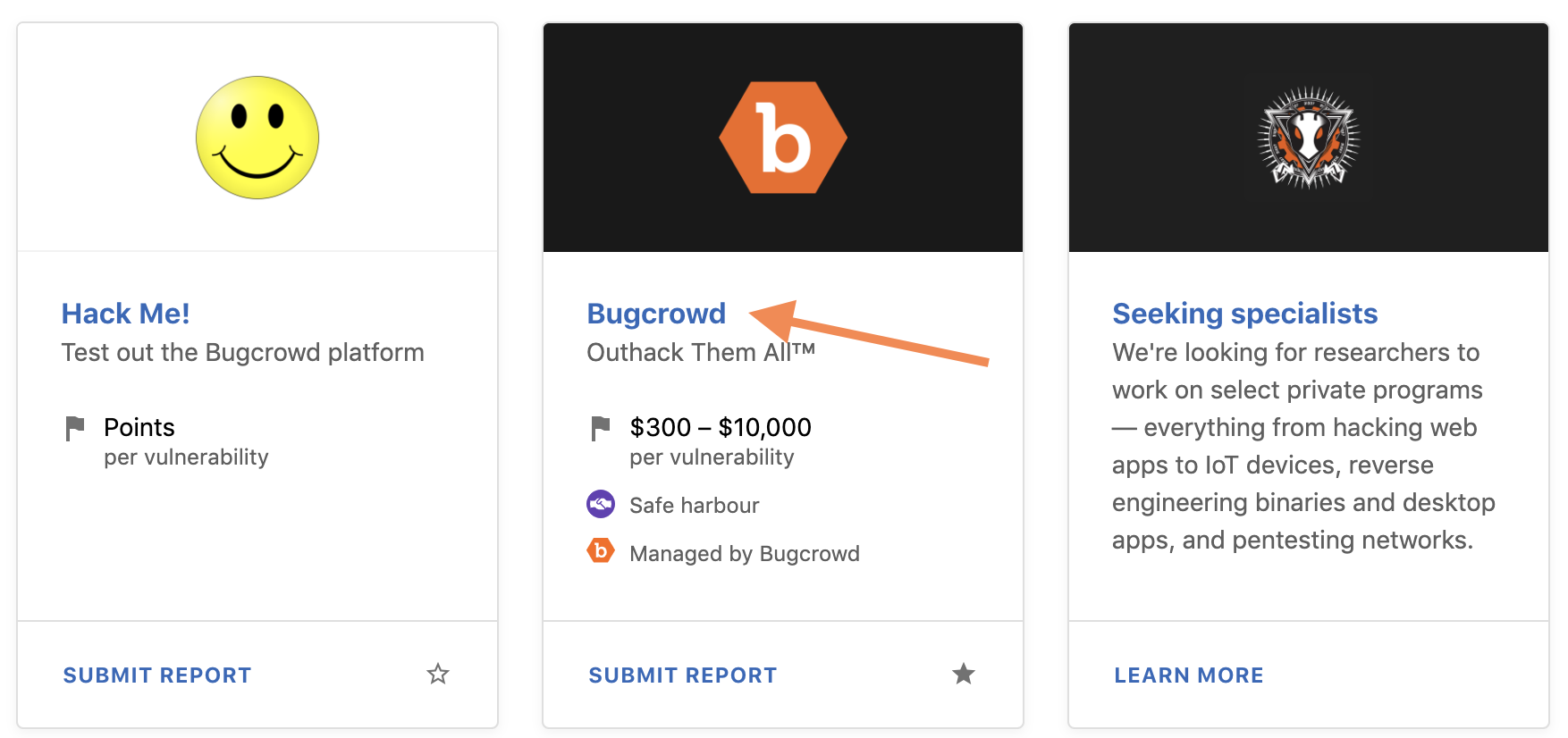
Viewing the Bounty Brief
To view the bounty brief for a particular program, go to the Programs list.

Click on the program name to view its bounty brief.
The bounty brief will look like a variation of this:
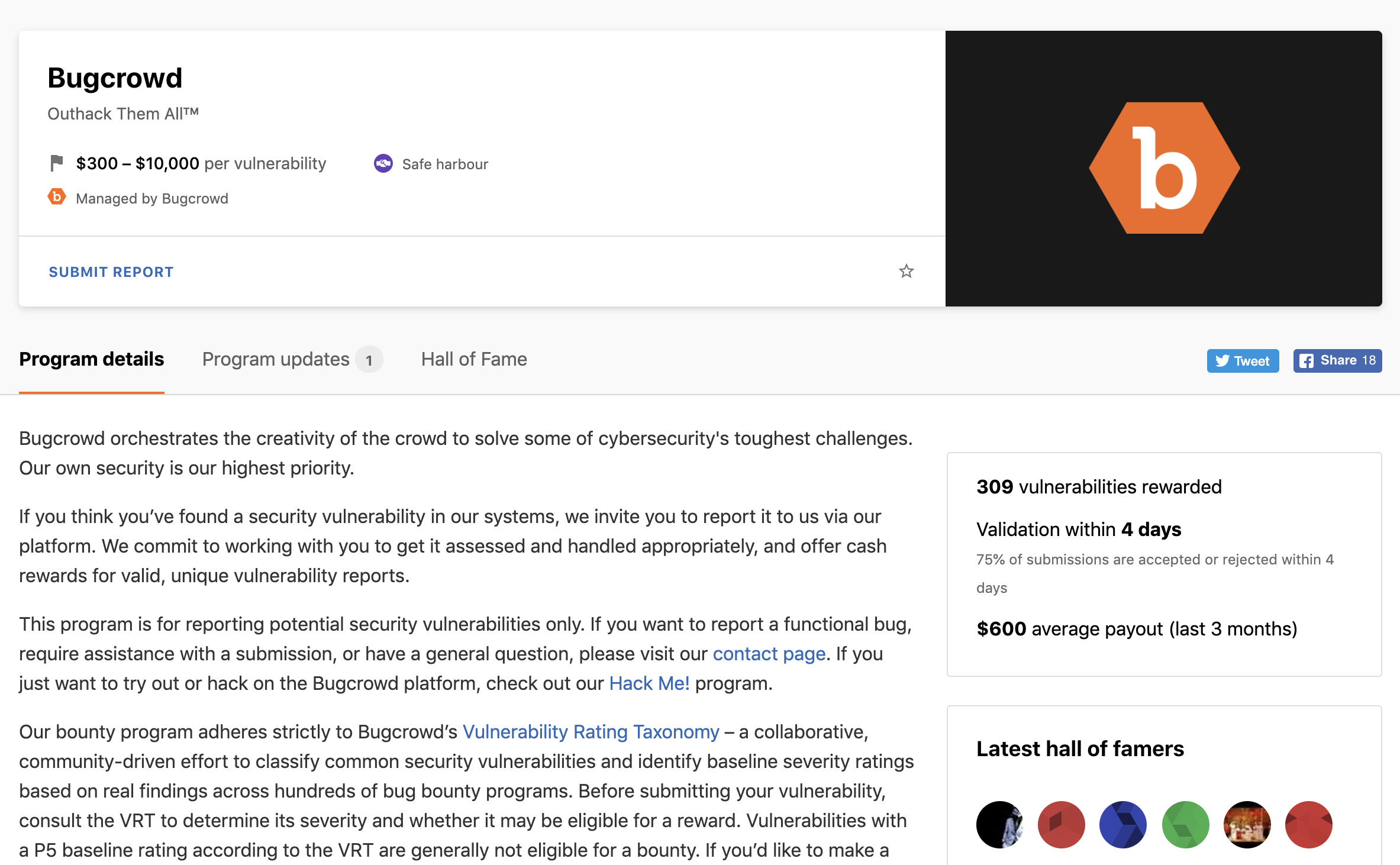
Each bounty brief differs depending on the needs of the company. At a minimum, it tells you the following information:
- The company overview.
- The targets you can test.
-
Areas the company wants you to focus on:
- Areas that are out of scope for testing.
- Additional rules that you must follow.
Always review the Bounty Brief before beginning testing: This helps prevent Out of Scope submissions. Reporting a vulnerability against a target not explicitly in scope may result in your report being marked as Out Of Scope, with a penalty of -1 point applied to your profile. If you have any questions about the scope of the program, submit a support ticket through the Bugcrowd Support Portal.
VDP Programs: When viewing program brief for VDP programs, a call-out is displayed on the right-side indicating that VDP programs no longer offer point rewards for submissions. For more information, see https://www.bugcrowd.com/blog/how-bugcrowd-sees-vulnerability-disclosure-programs-and-points/.
Now we will walk through different parts of the bounty brief you might see on a program.
Program Brief header
Identifying a Managed by Bugcrowd program
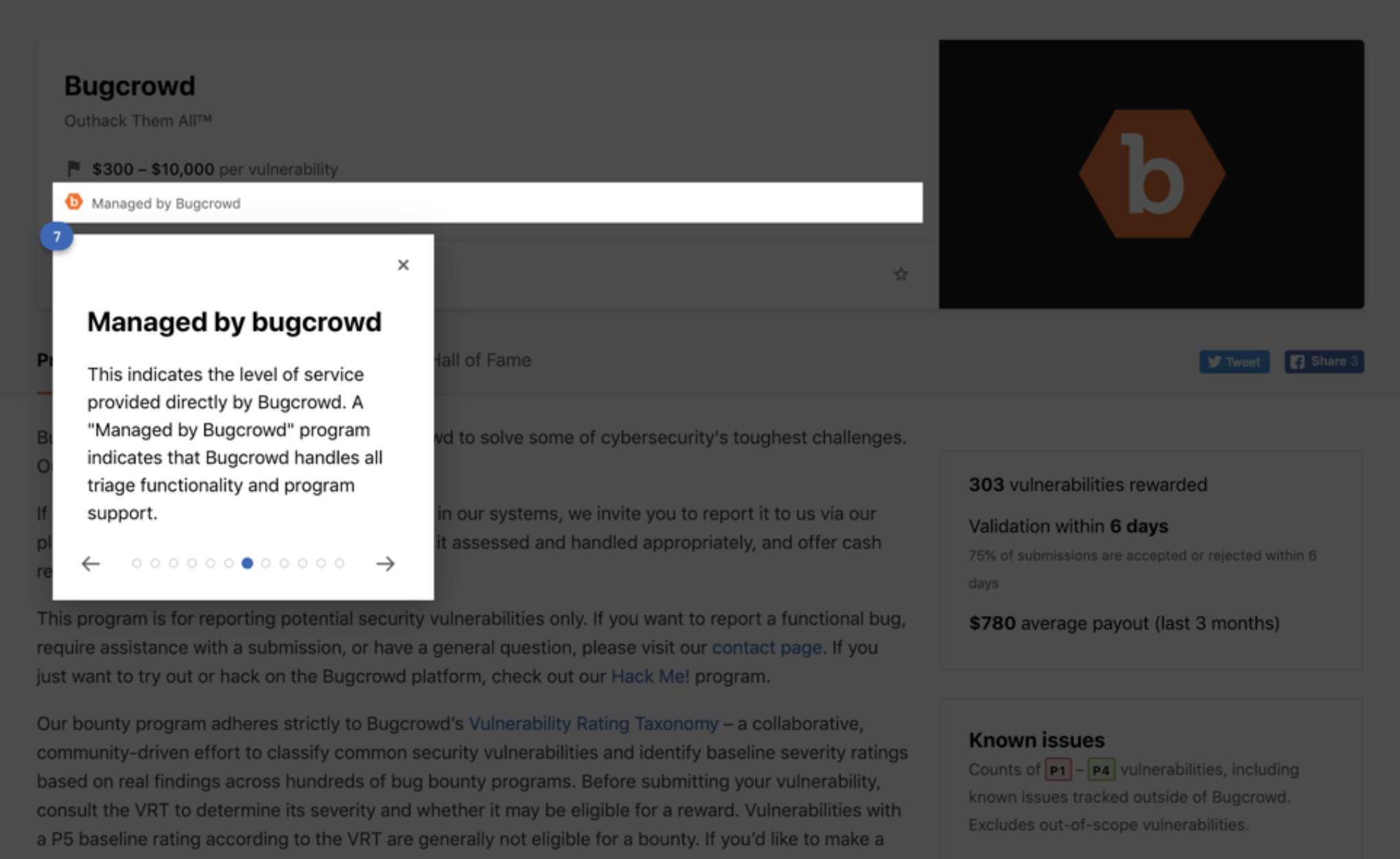
This designation lets you know who the program is managed by Bugcrowd, meaning our team handles triage and support. The majority of programs on the platform are managed by Bugcrowd.
Following a Program
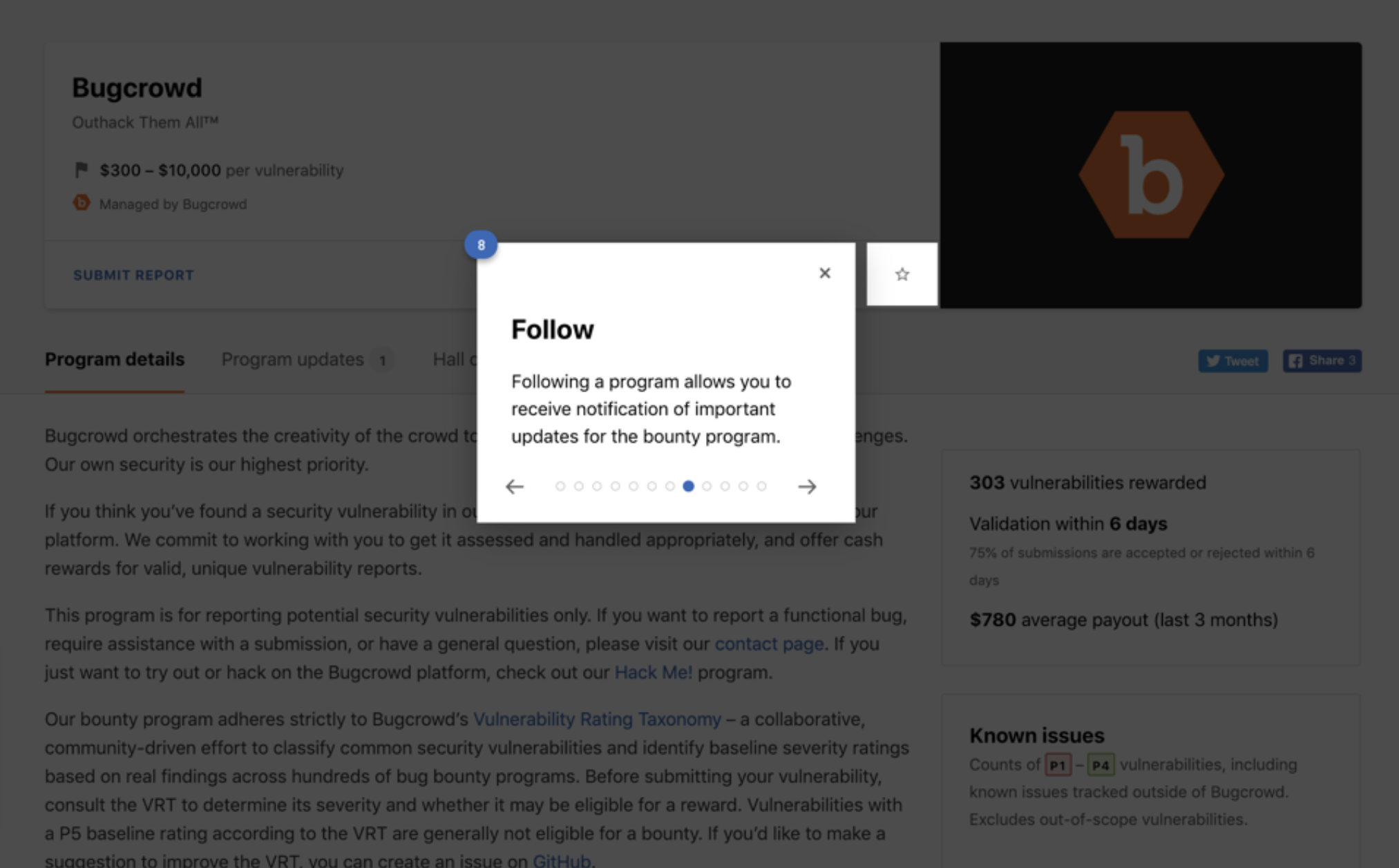
Following a particular program will provide you with email notifications of any important changes made on that program. These emails will include details on the exact changes made (ie Reward increases, or new targets or exclusions) and will also provide a link to the ‘Program Updates’ page. There you can find more details on any particular changes made on that specific program.
You will automatically follow a program once you submit your first report to that specific program or upon accepting an invitation to a private program.
For more in-depth information on following a program, see managing program subscriptions.
Reward Ranges
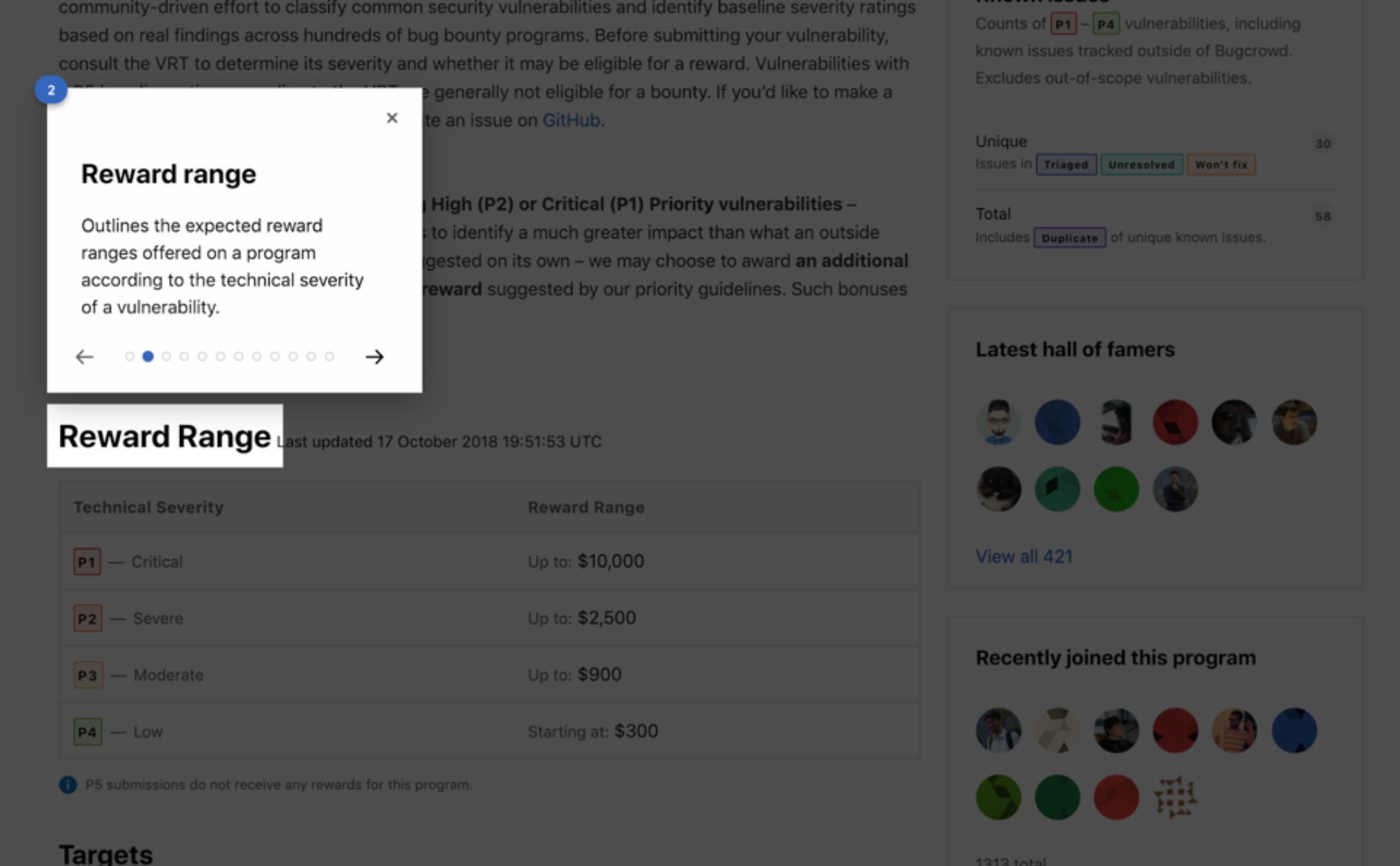
Reward ranges determined by vulnerability technical severity will be outlined in this section. There may also be specific conditions for rewards or vulnerabilities.
Scope and Rewards
In scope targets are the locations that you can test and submit vulnerability reports. Out-of-scope targets are the locations that you must not test.
The target and reward (if applicable) specifics include:
- In/Out of scope definitions
- Technology included within the targets
- Target details such as documentation links
- Reward range (if applicable)
Make sure that you only submit vulnerabilities for in-scope targets to avoid invalid or other submission results.
Out of Scope testing is prohibited: Testing the out-of-scope targets can result in platform escalations that may end in a ban. See the in-scope target groups for the locations you can test. If you have any questions, submit a support ticket through the Bugcrowd Support Portal.
The Scope and Rewards section displays at least one In scope and Out of scope target groups, but the program may segment rewards based on the target. You can view this through multiple in-scope target groups, each with their own reward ranges.
The following image shows one in-scope target group and an out-of-scope target.
The following image shows two in-scope target groups and an out-of-scope target.
Program Rules
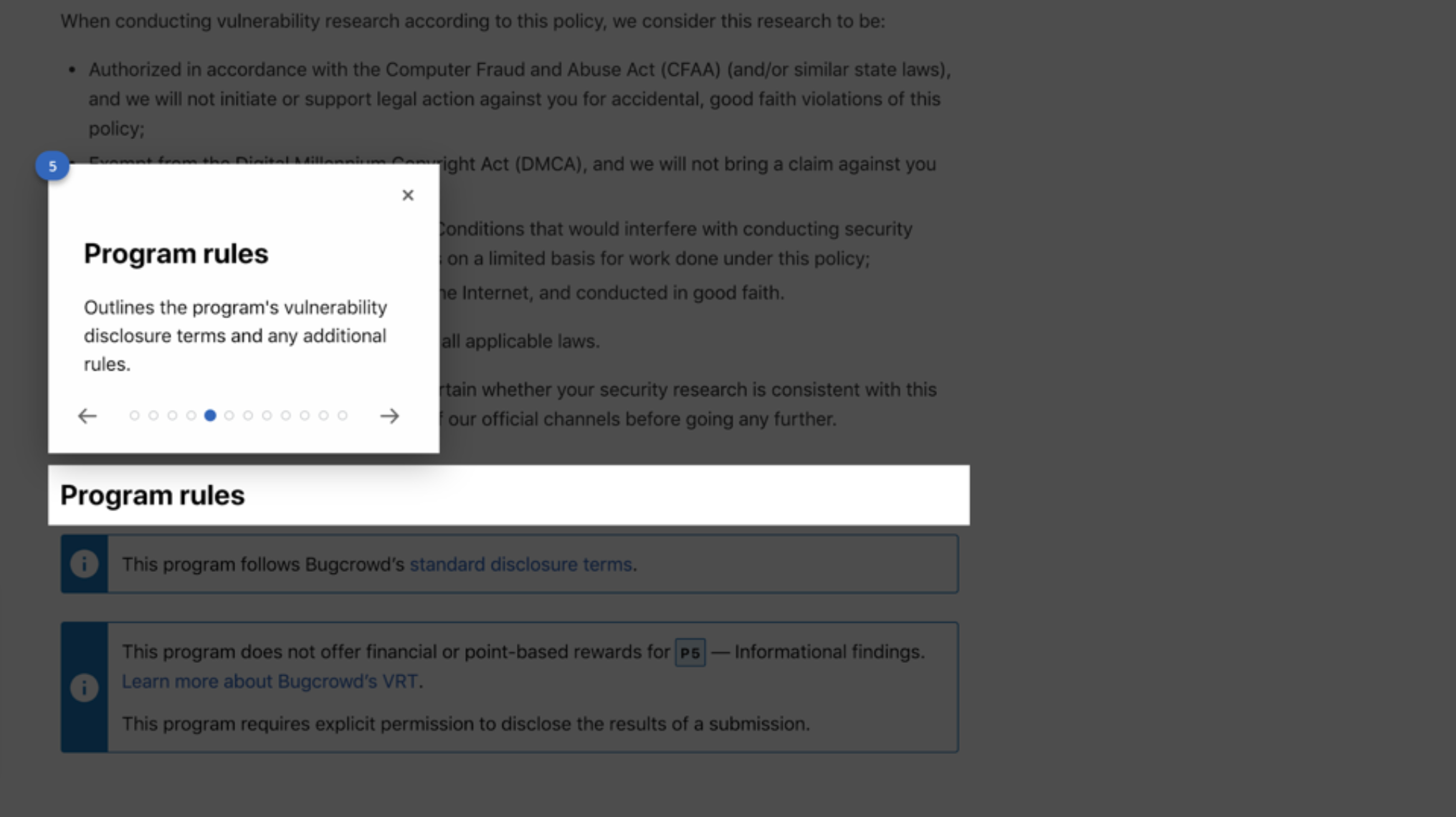
Program rules provide the disclosure terms and outline any specific rules that need to be followed for this program. If you have questions about the program rules, please contact our support team by submitting a support ticket through the Bugcrowd Support Portal.
It may be tempting to share your findings with others, but remember, each program has a disclosure policy that you must respect. Many programs do not want you to share the vulnerabilities that you’ve discovered with the public. Additionally, talking about a private program with another researcher who may not have been invited to the program is against the policies of Bugcrowd, as it discloses the existence of the program. Be smart, don’t do it.
For more information on disclosure policies for Bugcrowd programs, see our Public Disclosure Policy page.
Program Updates
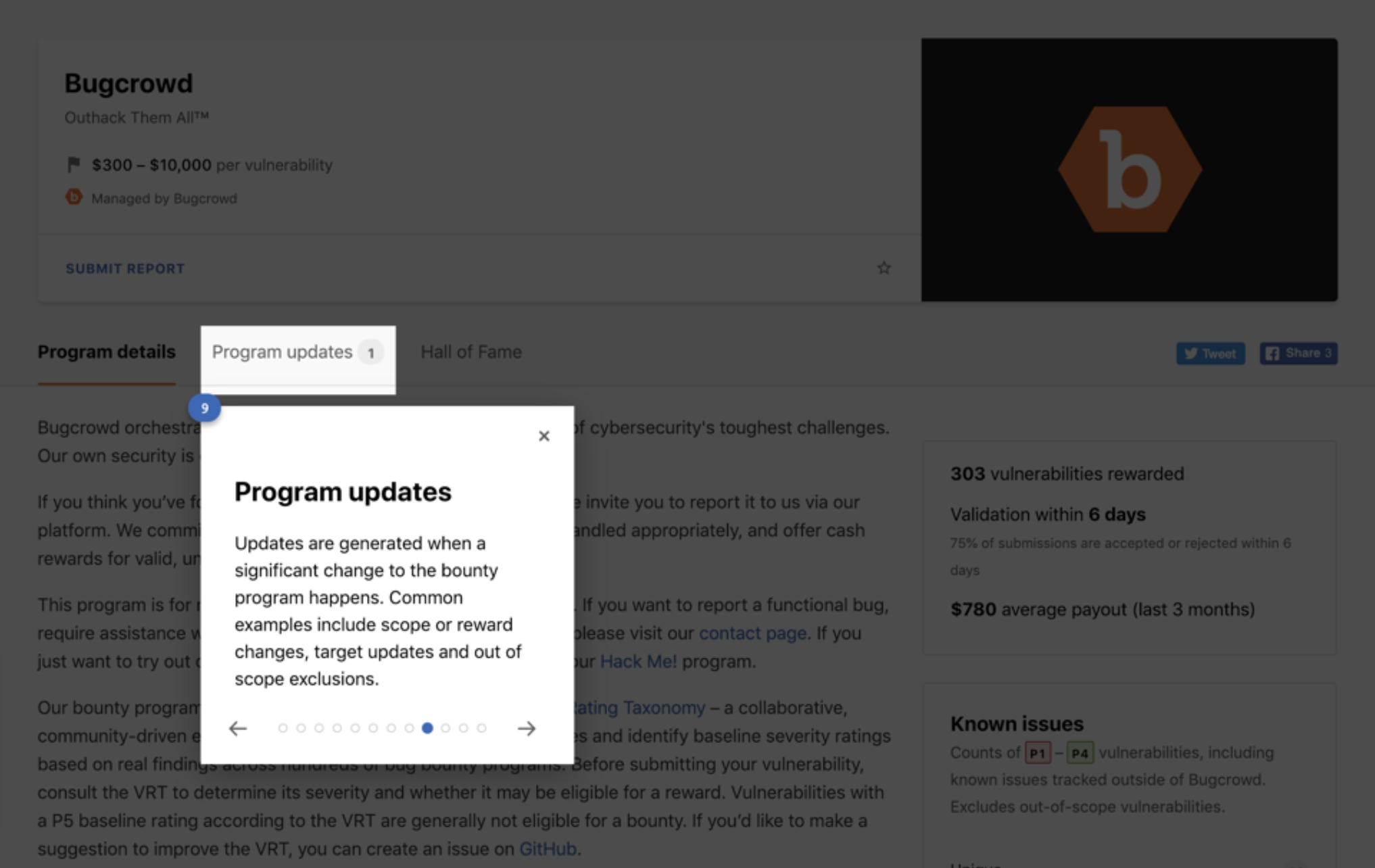
This section will provide you with all the recent and past important updates which have been made to the program.
Viewing the Program’s Statistics
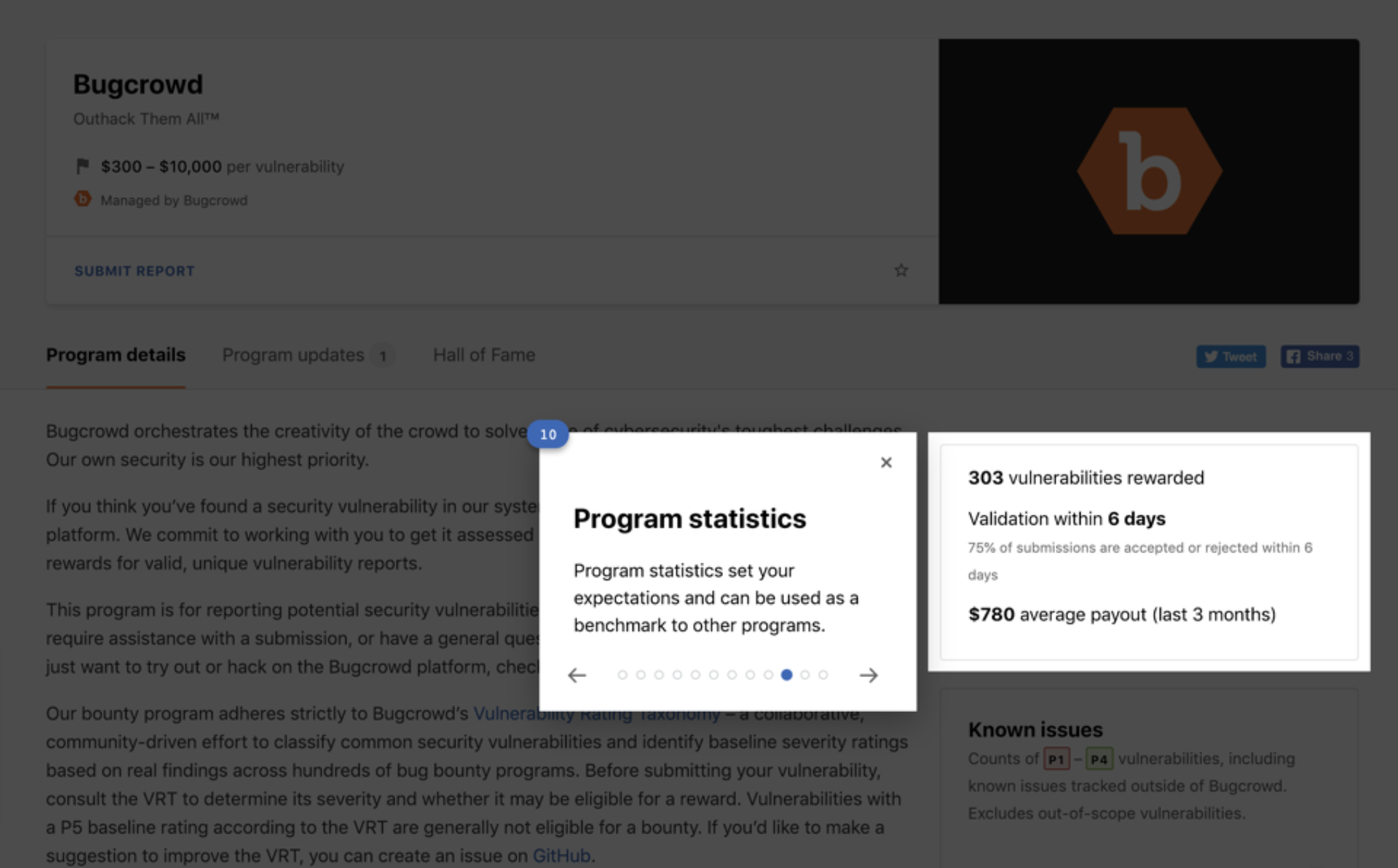
Each program provides you insights into the rewards that have been distributed and the validation time for submissions.
Viewing Known Issues
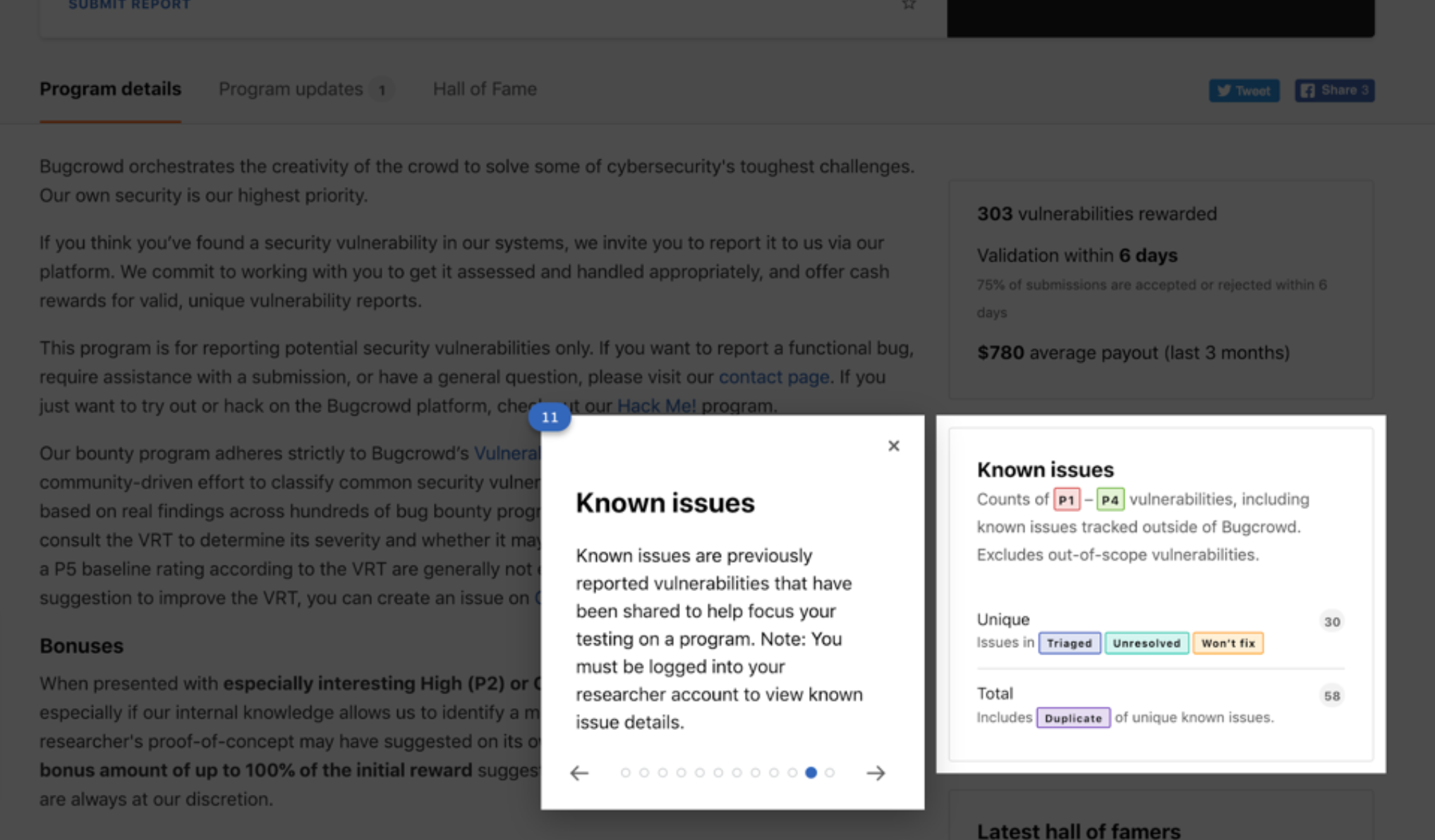
This section provides information on previously reported vulnerabilities for the program so that you choose how to concentrate your testing, on other areas that have not been previously reported or by choosing to focus in a specific area more deeply.
For additional information, see viewing known issues..
You must be signed into the platform in order to be able to view Known Issues available on Public Programs.
Hall of Fame
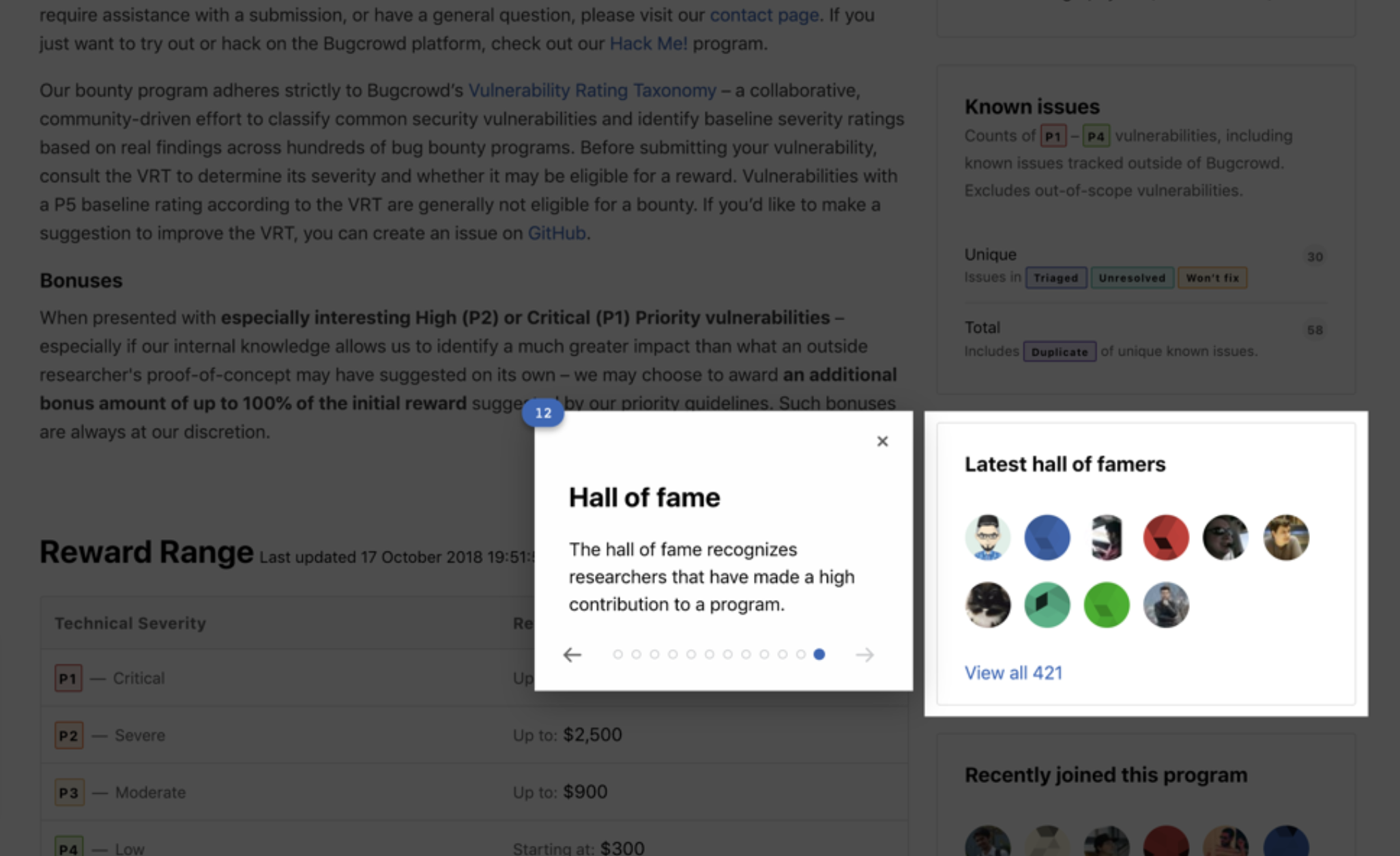
Finally, Public programs include this section which shows Researchers that are in the Hall of Fame for this program. Read about entering a Program’s Hall of Fame in detail.
