Bugcrowd offers a Security Assertion Markup Language (SAML) based Single Sign-On (SSO) integration with Okta, Centrify, OneLogin, Ping Identity, and Google to help you create an easy and centralized way to log in to Crowdcontrol. SAML is an XML-based standard for SSO authentication that creates a simplified way to access the applications that you can use.
Specific Role Required to Configure SSO: To configure SSO for your program, you must be an Organization Owner. Organization Owners can log in using Username and Password.
To setup SSO through SAML:
-
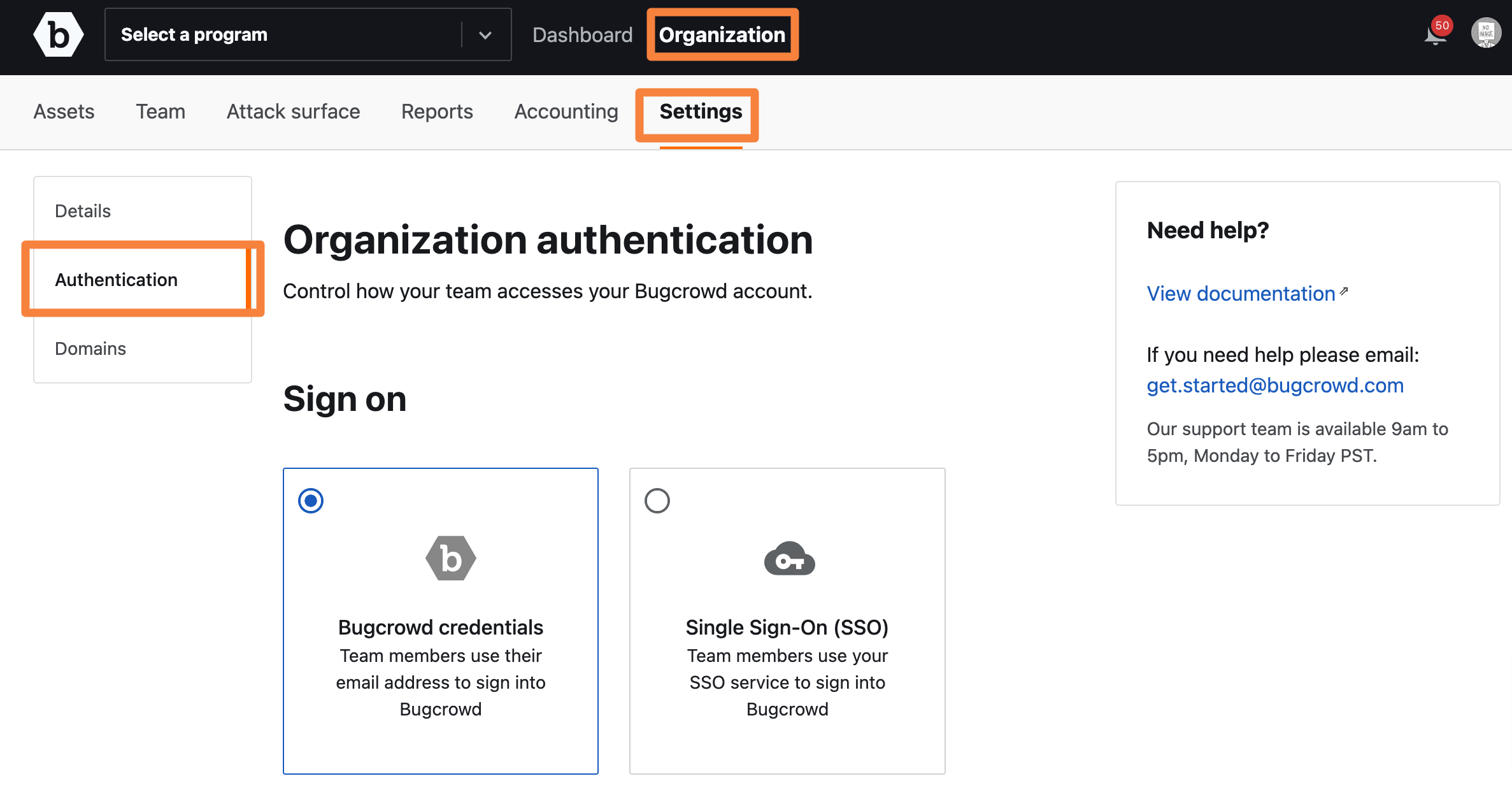
In Crowdcontrol, go to Organization, click Settings, and then click Authentication.
-
Click Single Sign-on (SSO).
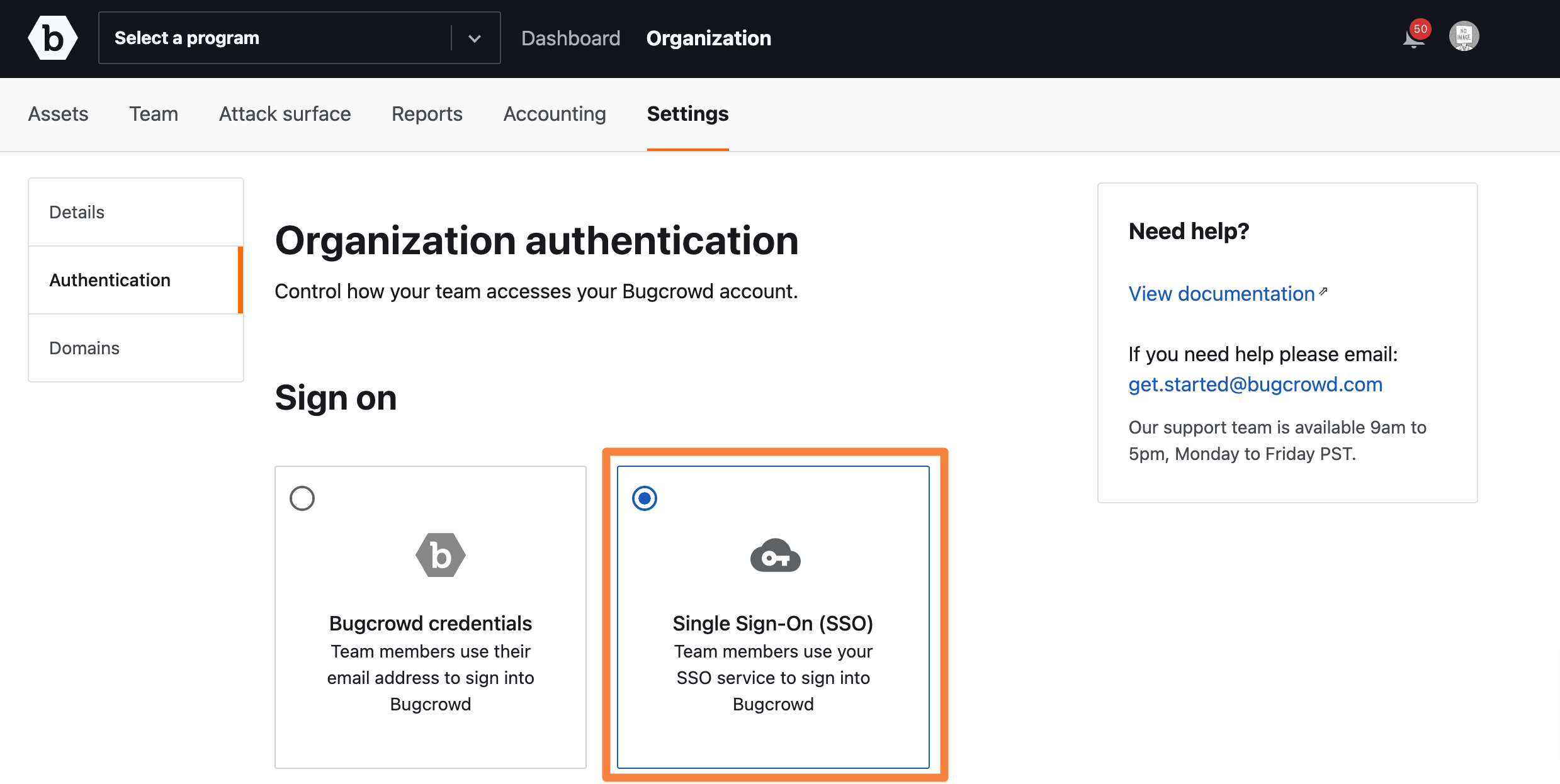
The Single Sign-On Settings section is displayed.
-
Make a note of the Single sign on URL and SP Entity ID.
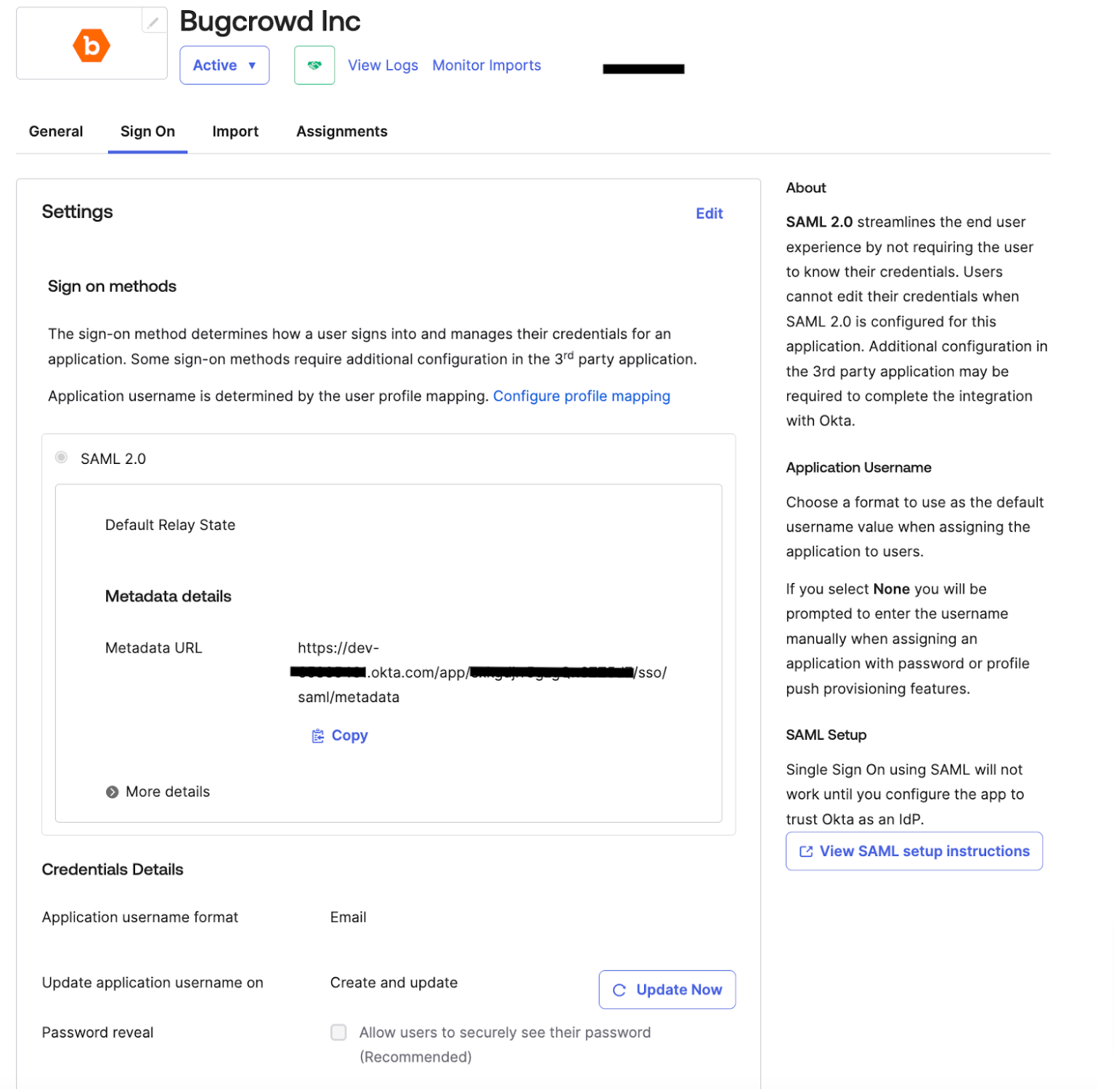
This information is required for adding Crowdcontrol to your third-party account.
Single Logout: Bugcrowd only supports logouts Identity Provider (IdP) initiated logouts, that is logging out of Bugcrowd will not log you out of your SSO provider.
-
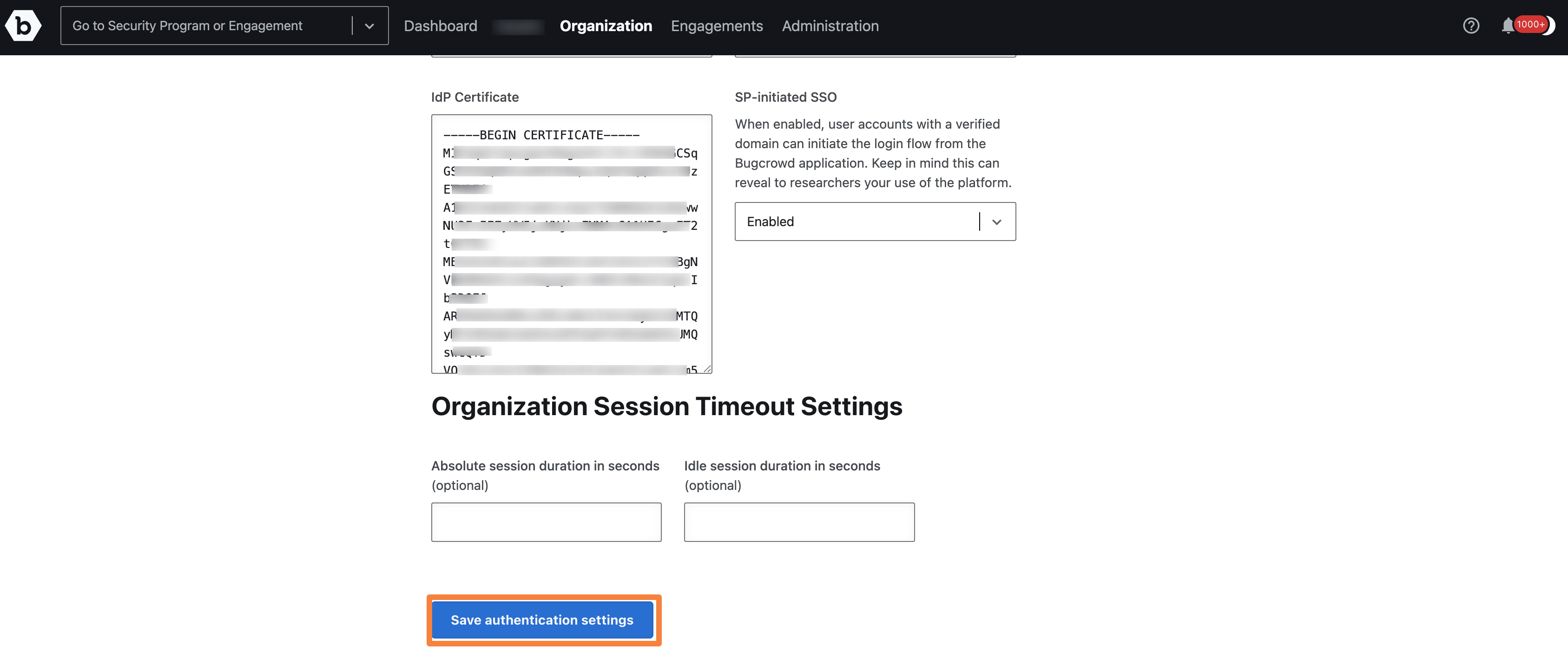
In the SAML Settings section, you must add information from the third-party tool for the following fields:
- IdP Entity ID
- IdP SSO Target URL
- IdP Certificate

-
Click Save authentication settings.
Verifying Domain
After setting up SSO, all the domains must be verified by Bugcrowd. You will not be able to log in until the email address domains are verified.
-
In Crowdcontrol, go to Organization, Settings and then click Domains.
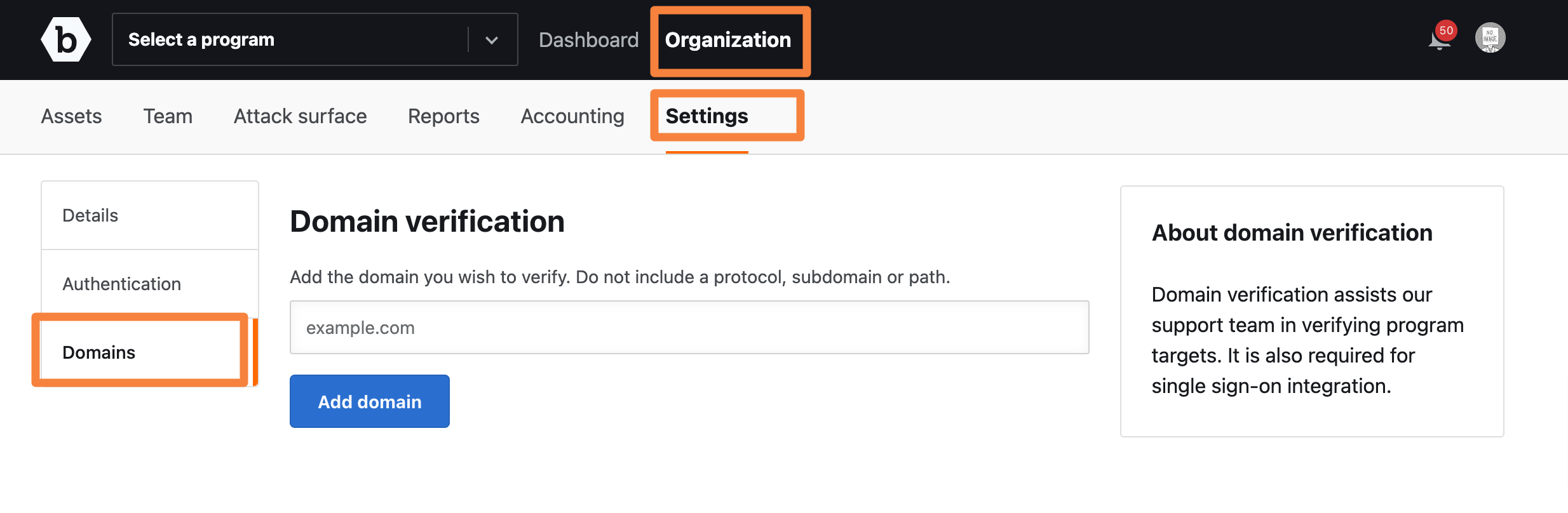
The Domain verification page is displayed.
-
Specify the domain and click Add Domain.
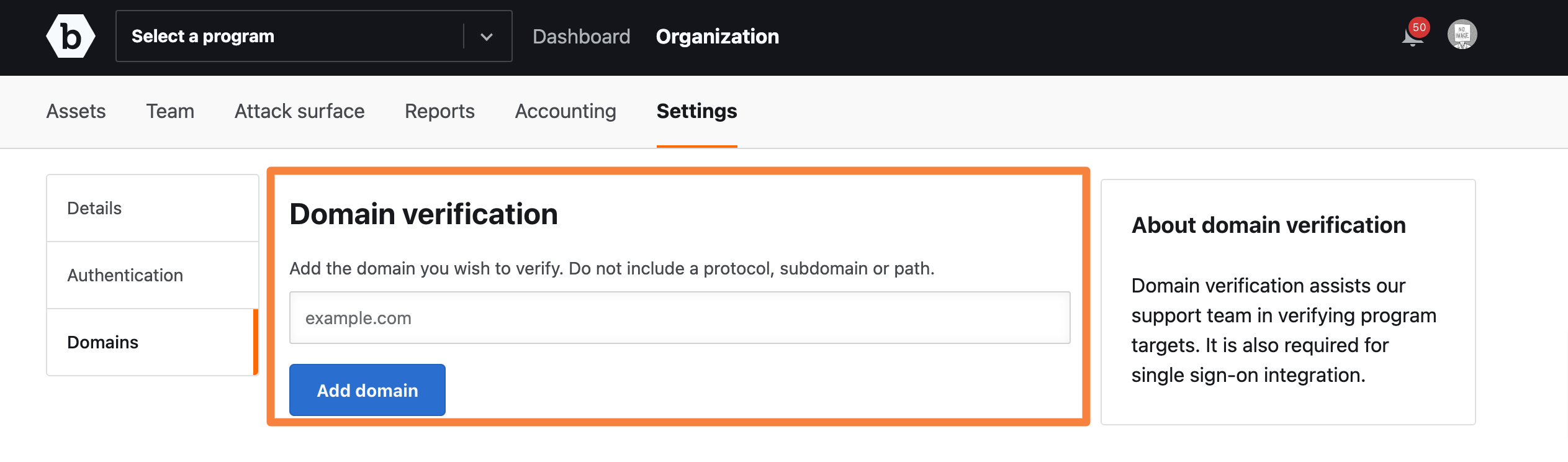
A verification code is displayed.
-
Add a TXT record at the domain’s root with this code.
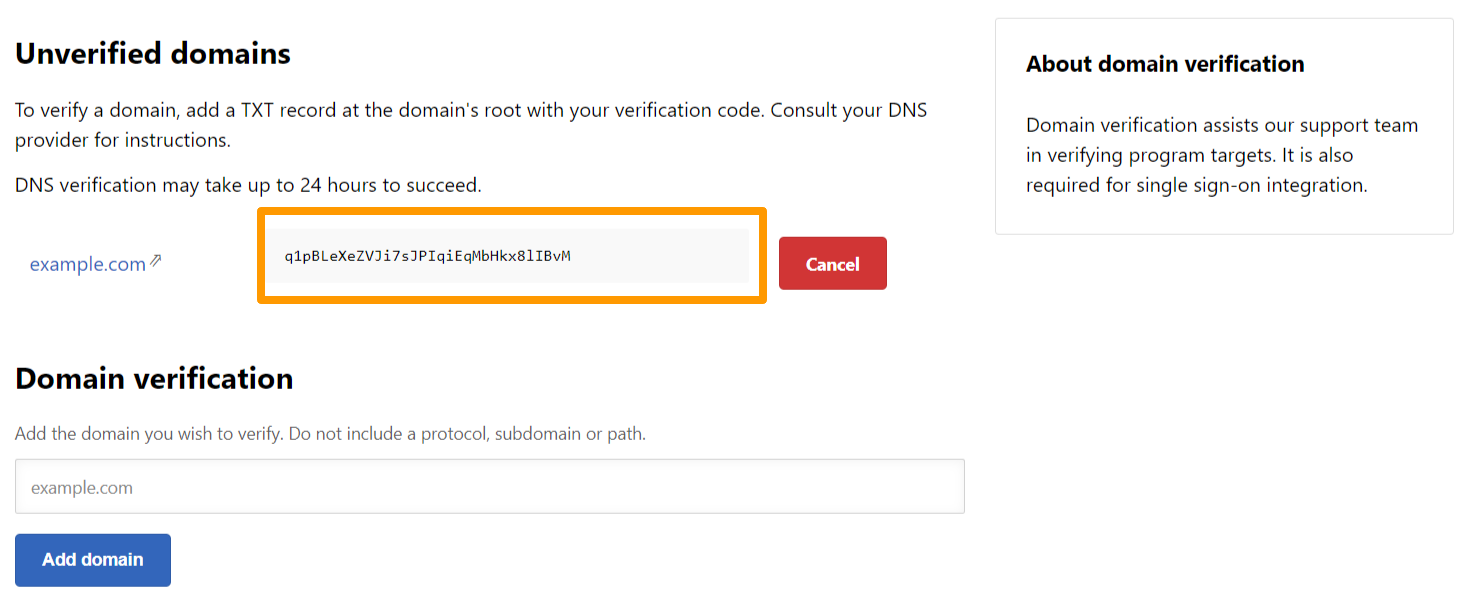
DNS verification may take up to 24 hours to succeed.
For information about adding a TXT record, consult your DNS provider. For any additional help verifying domains, submit a support ticket through the Bugcrowd Support Portal.
SSO Enforcement
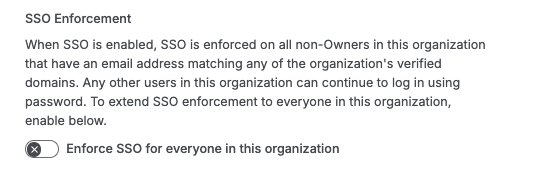
By default, when SSO is enabled for an organization, Bugcrowd does not enforce SSO for all members of your organization: Organization Owners, and members of your organization whose email domain has not been verified by the organization can still use username/password to log in.
If you want SSO to be enforced for all organization members (including the excluded categories above), then we provide the option of enabling “Enforce SSO for everyone in this organization”
Enabling this setting will enforce SAML on all users in your organization, regardless of whether they are an organization owner, or whether their email domain has been verified by the organization.
Bugcrowd requires domain verification to enable users on an email domain to sign in via SSO. This means if a user of your organization has an email address with a domain that your organization has not verified, enabling this feature will stop them from signing in to the Bugcrowd platform entirely. You may wish to check what domains you have verified, and what domains your organization members email addresses are using before enabling this feature.
