Types of Reports
You can generate the following types of report:
Viewing a Report
In the email you have received from Bugcrowd, click View Report.
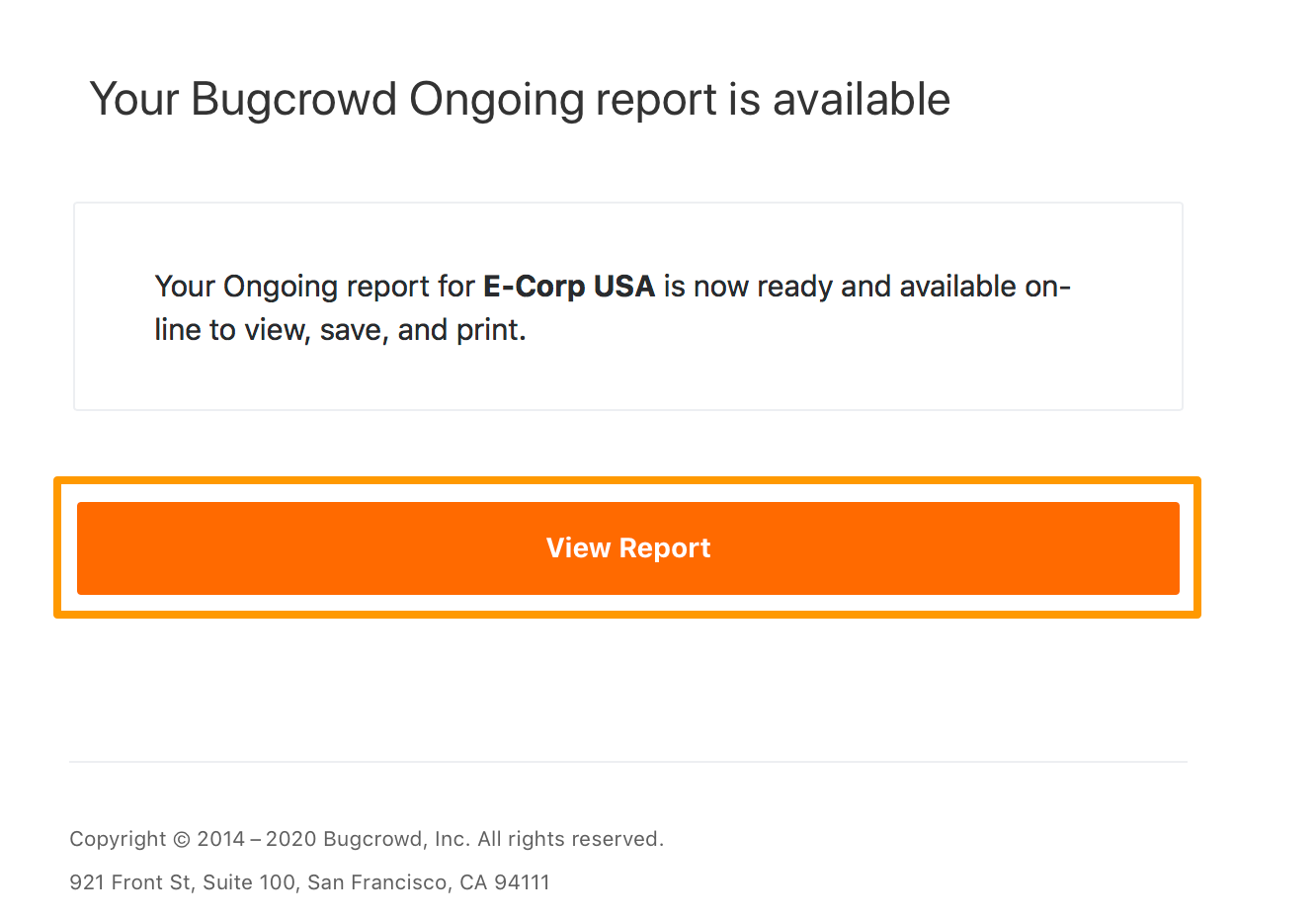
The report (in PDF format) opens in a browser and you can download the file.
You can also click the report title to view the report.
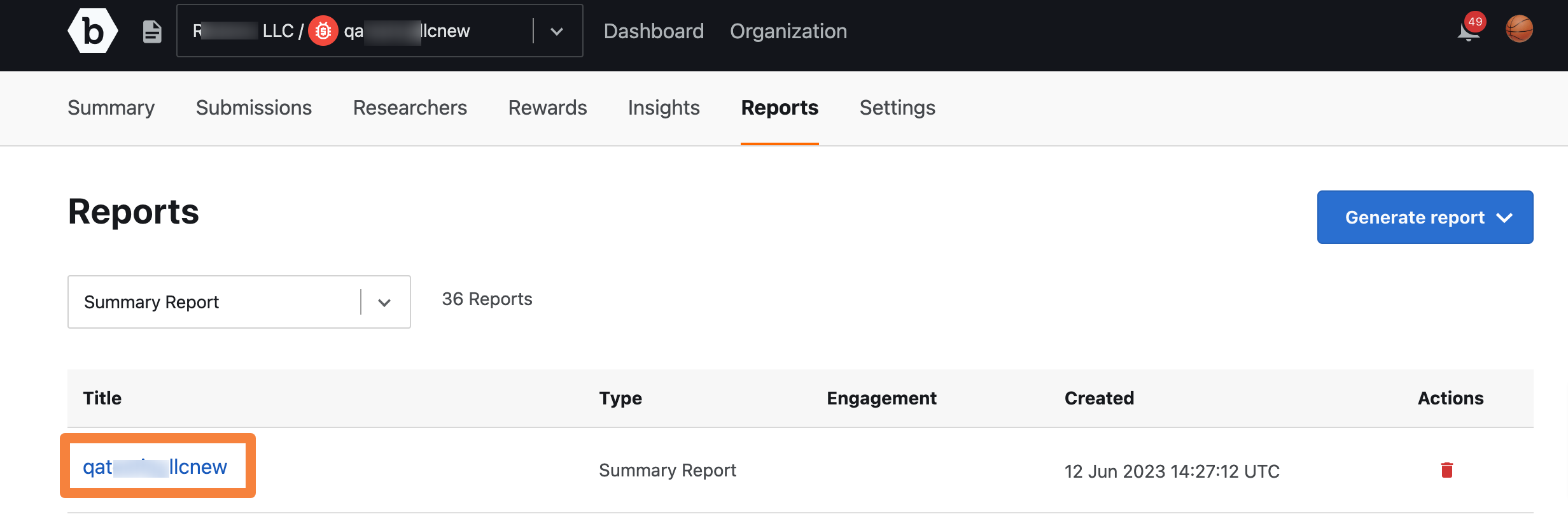
Note: The report title link is active only after the PDF report is generated.
Deleting a Report
Click the Delete icon for the report you want to delete.
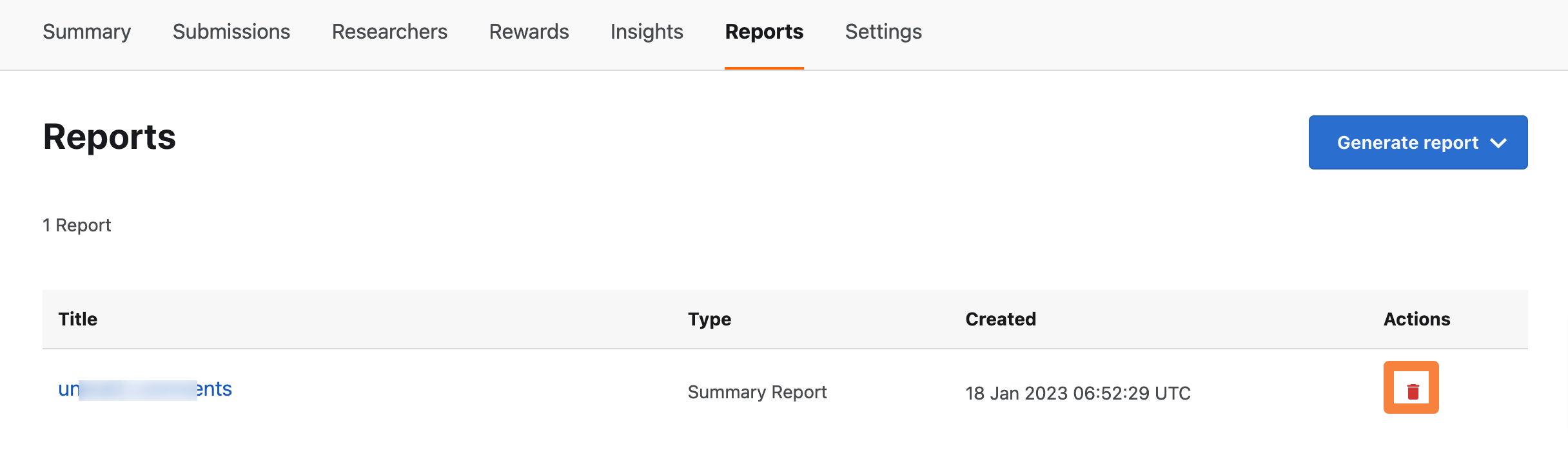
The Report deleted message is displayed.
